23/09/22
Understanding the Wintermute Hack
Category
Written by
Read time
3 min
Wintermute, a crypto asset manager and liquidity provider, was recently hacked for US$160m. The hack occurred on their DeFi operations and did not affect other operations, according to Wintermute CEO Evgeny Gaevoy.

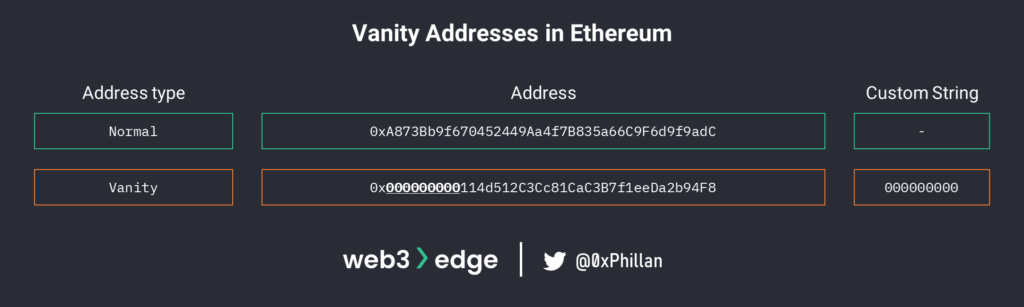
In this blog post, Mudit Gupta, Chief Security Officer at Polygon, points towards a vanity address generator called Profanity as being the source of the hack. A vanity address is an address which contains a user-defined character string. In Ethereum, the characters in addresses are limited to numbers and letters from A to F.
So, what happened?
Short answer
An Ethereum vanity address owned by Wintermute was compromised, which had admin privileges on a smart contract that controlled its DeFi funds.
Long answer
Let’s break down this hack using Mudit Gupta’s blog post, @YettyWapp’s Twitter thread and other news emerging as I write this.

On Jun 17th suspicious activity was detected on multiple deployer addresses. A deployer address is an externally owned address, also called EOA, which is an address created and used by a human, and not a smart contract. These unrelated deployer addresses claimed an airdrop for $FORTA and sent them to the same EOA address. That address dumped the airdrop for ETH tokens. This activity suggests one attacker was able to access multiple addresses, which points towards a common vulnerability.
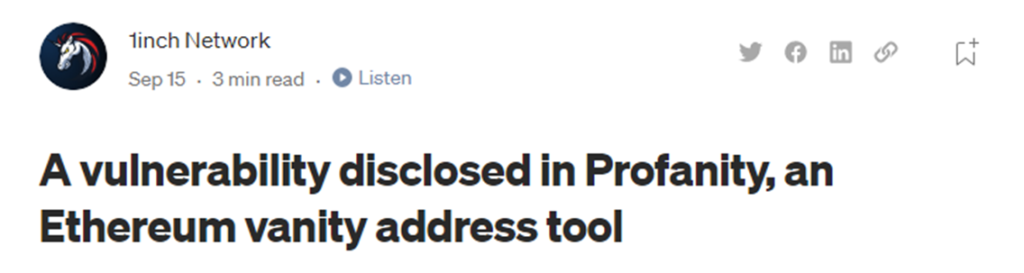
On Sep 17th the 1inch blog warned that addresses generated using the Profanity vanity address generator may be compromised, after it was found that addresses generated using the tool could be brute forced with the public key alone by reversing Profanity’s vanity address generation process.
When you generate a new Ethereum address and share it with other people, they cannot guess the public key from the address alone. However, as soon as you initiate a single transaction, the public key becomes visible on chain through the transaction signature.
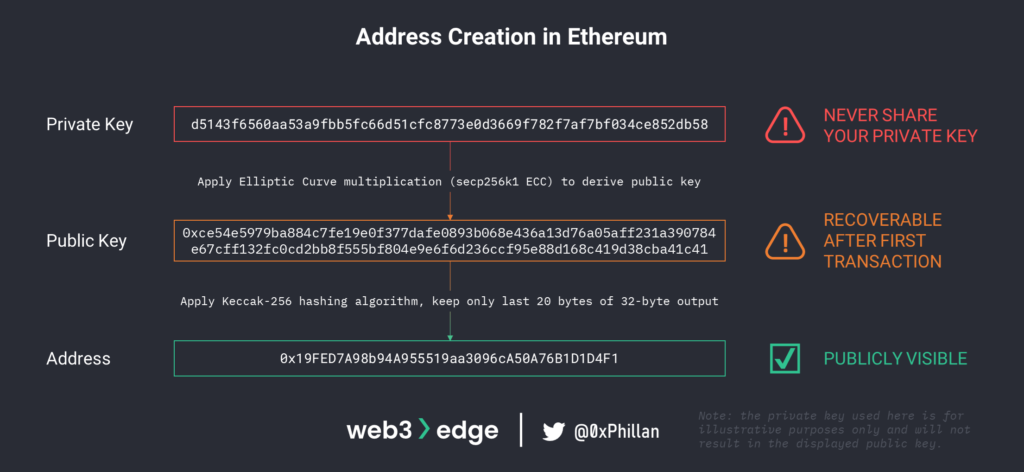
This means that as soon as the vanity address that was used to deploy the Wintermute vault smart contract, the public key became recoverable and the Profanity bug could be exploited.
Around the same time as the 1inch blog post, the remaining ether inside the vanity address was moved to another address; Evgeny points out that they were aware of this exploit and accelerated retiring less secure accounts.

Without any Ether in the address, the address cannot interact with the vault smart contract, since it needs to pay gas fees using Ether.
On Sep 20th, the attacker transferred 2 Ether into the vanity address. The vault smart contract has a setting to designate Ethereum addresses as administrators. Mudit explains that because the vanity address was never removed as an administrator, the address had full access to the vault smart contract.
With full access to the vault smart contract, the exploiter could interact with the vault and move out all funds to their personal wallet.
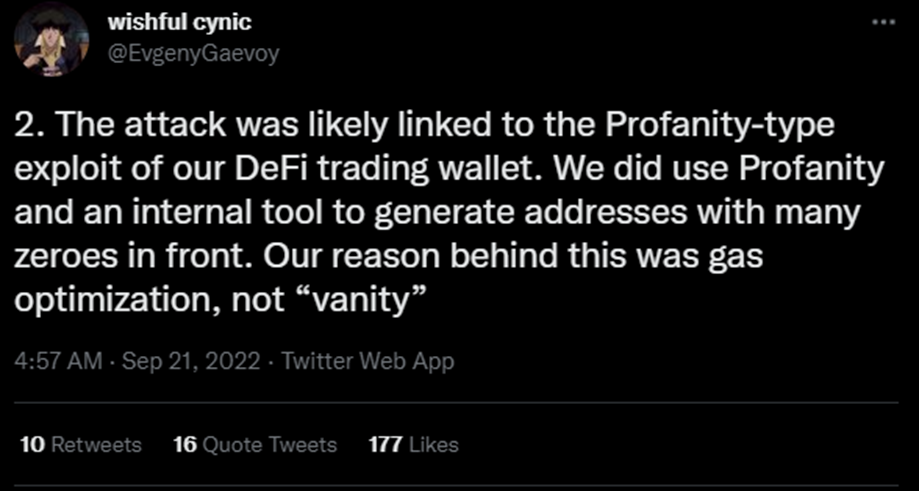
While Wintermute’s vanity address has been compromised, as of time of writing it has not yet been conclusively confirmed that this was a result of the Profanity bug. However, this appears to be most likely, with Wintermute CEO Evgeny Gaevoy suggesting the same and confirming their use of Profanity.
In his blog Mudit also writes:
“The attacker is likely a seasoned hacker/solidity developer. They created a helper contract, deposited stables into curve to avoid blacklisting, and figured out this vulnerability in a closed sourced vault contract in the first place.”
Despite the hack, Evgeny says that they are still solvent with over twice the amount of equity left. To come to an amicable agreement with the hacker, Evgeny proposes the hacker return a majority of the stolen funds and keep 16m USDC for themselves.
SHARE THIS PIECE
Related content
In this piece @lingchenjaneliu explores the staking market landscape, including key actors and top players, as well as latest developments in Proof-of-Stake. Special thanks to @0xPhillan for ...
The year of 2022 was a year of great highs and new lows for the Web3 industry. Read more about the defining events of 2022!
Metaverse Concept and History The term "metaverse" was invented by American author Neal Stephenson in his science fiction novel titled Snow Crash, published in 1992. ...
Short answer: Account abstraction creates a new account type which exists as a smart contract. By having the account exist as a smart contract, transaction ...